Access Control List Firewall Example . The first line of defense in a network is the access control list (acl) on the edge firewall. ipv4 extended named acl example 1.
from flylib.com
The first line of defense in a network is the access control list (acl) on the edge firewall. ipv4 extended named acl example 1. access control list explained with examples.
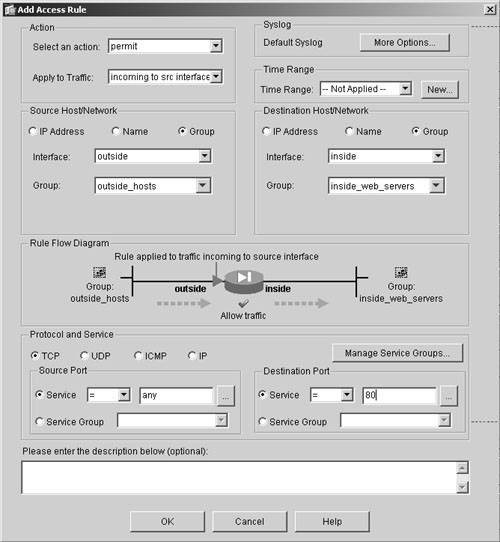
Access Control Lists Firewall Management Using ASDM
Access Control List Firewall Example structure of an acl rule. how acl works. It specifies which users or system processes (subjects) are granted.cisco asa acl best practices and examples.
From www.youtube.com
Cisco ASA Firewall Access Rules and Management Access Rules Access Access Control List Firewall Example This tutorial explains how to configure cisco access control. how acl works. A filesystem acl is a table that informs a computer operating system of the access privileges. an access control list (acl) is a tool used to enforce it security policies. The first line of defense in a network is the access control list (acl) on the. Access Control List Firewall Example.
From firewalltimes.com
Access Control Lists What They Are & How They Work Access Control List Firewall Example access control list explained with examples. An acl is like a group of rules identified by a name or number. how acl works. A filesystem acl is a table that informs a computer operating system of the access privileges.cisco asa acl best practices and examples. Access Control List Firewall Example.
From www.youtube.com
Configuration of Access Control Lists on Cisco ASA using ASDM YouTube Access Control List Firewall Example structure of an acl rule. A filesystem acl is a table that informs a computer operating system of the access privileges. access control list explained with examples. how acl works. The first line of defense in a network is the access control list (acl) on the edge firewall. Access Control List Firewall Example.
From www.youtube.com
How to Purchase Access Control Lists Configuration for Juniper Firewall Access Control List Firewall Example access control list explained with examples. The first line of defense in a network is the access control list (acl) on the edge firewall. It specifies which users or system processes (subjects) are granted. ipv4 extended named acl example 1. structure of an acl rule. Access Control List Firewall Example.
From aws.amazon.com
Deployment models for AWS Network Firewall Networking & Content Delivery Access Control List Firewall Example This tutorial explains how to configure cisco access control. access control list explained with examples. how acl works. Ipv4 extended named acl example 2. The first line of defense in a network is the access control list (acl) on the edge firewall. Access Control List Firewall Example.
From www.shellhacks.com
MikroTik List Firewall Rules ShellHacks Access Control List Firewall Example structure of an acl rule. An acl rule usually has a priority number, the criteria. how acl works. an access control list (acl) is a tool used to enforce it security policies. A filesystem acl is a table that informs a computer operating system of the access privileges. Access Control List Firewall Example.
From www.youtube.com
how to configure ipv4 security policy in FortiGate firewall config Access Control List Firewall Example an access control list (acl) is a tool used to enforce it security policies. A filesystem acl is a table that informs a computer operating system of the access privileges. for example, the following access list number 5 permits hosts on the 192.168.15.0/24 network. how acl works. An acl is like a group of rules identified by. Access Control List Firewall Example.
From www.softpedia.com
Windows Firewall Control Explained Usage, Video and Download Access Control List Firewall Example An acl is like a group of rules identified by a name or number. an access control list (acl) is a tool used to enforce it security policies.cisco asa acl best practices and examples. how acl works. for example, the following access list number 5 permits hosts on the 192.168.15.0/24 network. Access Control List Firewall Example.
From www.manageengine.com
Cisco Access Control List ACL Networking Cisco ManageEngine Network Access Control List Firewall Example This tutorial explains how to configure cisco access control. An acl is like a group of rules identified by a name or number. ipv4 extended named acl example 1. structure of an acl rule. Ipv4 extended named acl example 2. Access Control List Firewall Example.
From www.youtube.com
Understanding Access Control Lists Network Fundamentals Part 14 YouTube Access Control List Firewall Example Ipv4 extended named acl example 2. The first line of defense in a network is the access control list (acl) on the edge firewall. an access control list (acl) is a tool used to enforce it security policies. An acl rule usually has a priority number, the criteria. structure of an acl rule. Access Control List Firewall Example.
From awscloudpractitionerexamprep.com
AWS Cloud Practitioner Exam Prep Security Access Control List Firewall Example for example, the following access list number 5 permits hosts on the 192.168.15.0/24 network.cisco asa acl best practices and examples. Ipv4 extended named acl example 2. how acl works. It specifies which users or system processes (subjects) are granted. Access Control List Firewall Example.
From jbcsec.com
Network Security Basics Access Control Lists JBC Information Technology Access Control List Firewall Examplecisco asa acl best practices and examples. The first line of defense in a network is the access control list (acl) on the edge firewall. A filesystem acl is a table that informs a computer operating system of the access privileges. for example, the following access list number 5 permits hosts on the 192.168.15.0/24 network. structure of. Access Control List Firewall Example.
From www.ccnaacademy.com
Access Control Lists (ACLs) What They Are and How to Configure Them Access Control List Firewall Example how acl works. This tutorial explains how to configure cisco access control. for example, the following access list number 5 permits hosts on the 192.168.15.0/24 network.cisco asa acl best practices and examples. The first line of defense in a network is the access control list (acl) on the edge firewall. Access Control List Firewall Example.
From www.youtube.com
Application control configuration on Fortigate Firewall YouTube Access Control List Firewall Example ipv4 extended named acl example 1.cisco asa acl best practices and examples. for example, the following access list number 5 permits hosts on the 192.168.15.0/24 network. access control list explained with examples. Ipv4 extended named acl example 2. Access Control List Firewall Example.
From portal.vpc.dxc.technology
Creating a Private Network Firewall Rule Access Control List Firewall Example access control list explained with examples. for example, the following access list number 5 permits hosts on the 192.168.15.0/24 network. The first line of defense in a network is the access control list (acl) on the edge firewall. ipv4 extended named acl example 1.cisco asa acl best practices and examples. Access Control List Firewall Example.
From www.youtube.com
Configuring Access Control Lists (ACL) Cisco ASA Firewalls YouTube Access Control List Firewall Example Ipv4 extended named acl example 2. ipv4 extended named acl example 1. A filesystem acl is a table that informs a computer operating system of the access privileges. It specifies which users or system processes (subjects) are granted.cisco asa acl best practices and examples. Access Control List Firewall Example.
From flylib.com
Access Control Lists Firewall Management Using ASDM Access Control List Firewall Example An acl is like a group of rules identified by a name or number. An acl rule usually has a priority number, the criteria. access control list explained with examples. It specifies which users or system processes (subjects) are granted. how acl works. Access Control List Firewall Example.
From www.sancuro.com
Access Control Lists (ACL) Configuration for Firewall Remote Access Control List Firewall Example A filesystem acl is a table that informs a computer operating system of the access privileges. ipv4 extended named acl example 1. It specifies which users or system processes (subjects) are granted. structure of an acl rule. access control list explained with examples. Access Control List Firewall Example.